Cryptocurrency enthusiasts find themselves at the crossroads of convenience and security, faced with the dilemma of choosing between hot and cold wallets. Hot wallets, residing on online platforms or exchanges, offer immediate access for trading and transactions, but at the expense of heightened vulnerability. On the other hand, cold wallets, including hardware and paper wallets, safeguard assets offline, providing a shield against digital threats. As the popularity of cryptocurrencies continues to rise and hackers become increasingly ingenious, the choice between these wallet types takes on new significance.
Preparing for the Transfer: Strengthening Your Wallet Arsenal
Before embarking on the journey to transfer your cryptocurrency funds from a hot wallet to the impregnable fortress of a cold wallet, there are several crucial steps you must undertake to ensure a seamless and secure transition.
Understanding Hot and Cold Wallets
Before embarking on the journey of transferring funds, it’s crucial to understand the fundamental difference between hot and cold wallets. Hot wallets, as the name suggests, are constantly connected to the internet. They include wallets on cryptocurrency exchanges and online platforms. While hot wallets offer immediate access and are suitable for frequent trading, they are susceptible to cyberattacks due to their online presence. On the other hand, cold wallets are offline storage solutions, making them inherently more secure. Hardware wallets are physical devices that store your private keys offline, while paper wallets involve printing out your keys and keeping them physically secure. Cold wallets are ideal for holding large amounts of cryptocurrencies over extended periods.

Factors Influencing Transfer Decisions
The decision to transfer funds from a hot to a cold wallet is influenced by several factors. First, consider the frequency of your trading or transactions. If you’re an active trader, keeping a portion of your funds in a hot wallet might be necessary for immediate access. However, if you’re a long-term investor, the security benefits of a cold wallet may outweigh the convenience. Your personal security concerns and risk tolerance also play a role. High-profile hacks and security breaches have led many to prioritize the safety of their assets. Additionally, the types of cryptocurrencies you hold can impact your decision. High-value assets are often better protected in cold storage.
Preparing for the Transfer
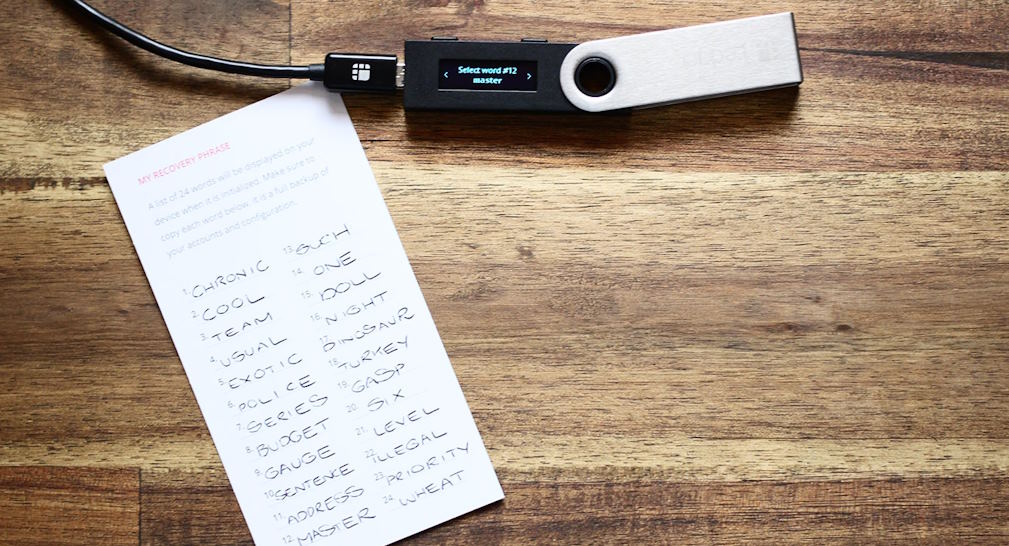
Before initiating the transfer, several crucial preparatory steps must be taken. Start by choosing a suitable cold wallet based on your preferences and needs. Hardware wallets offer robust security with an added layer of physical protection, while paper wallets provide an offline option without the need for specialized hardware. Download and set up the necessary wallet software, ensuring it comes from reputable sources to avoid potential malware. Strengthen your device’s security by enabling features like PIN codes and passphrases to prevent unauthorized access.

Step-by-Step Transfer Process
The actual transfer process involves several key steps to ensure the security and accuracy of your transaction. Begin by generating a receiving address within your chosen cold wallet. Then, initiate the withdrawal from your hot wallet, which might be an exchange account. Access your hot wallet and navigate to the withdrawal section. Paste the cold wallet’s receiving address and verify all transaction details, including the address itself and the withdrawal amount along with associated fees. Once you’re certain, approve and confirm the withdrawal, and patiently await the confirmation of the transaction on the blockchain.
Ensuring Security Throughout
Maintaining security during and after the transfer is paramount. Clear your clipboard and browsing history after copying sensitive information. Keep your private keys and recovery phrases offline and in secure locations. Regularly update your wallet software and firmware to stay protected against potential vulnerabilities. Consider implementing additional security layers like two-factor authentication (2FA) and dedicating devices solely for wallet transactions to minimize risks.