The increasing popularity of cold wallets – offline storage solutions designed to fend off cyber threats – highlights the need to understand and implement strategies that ensure consistent access to your digital funds. Recovery seeds, often underestimated and overlooked, form the linchpin of this access, allowing you to recover and restore your assets even if the physical storage medium is lost, damaged, or compromised.
Ensuring Security of Recovery Seeds
When it comes to safeguarding your cryptocurrency holdings, the security of your recovery seeds is paramount. These seeds hold the master keys to your digital assets, making their protection a critical concern. Here, we explore essential practices to ensure the utmost security for your recovery seeds.
Choosing a Secure Environment
- Offline and Air-Gapped Systems: Opt for generating and handling recovery seeds on devices that have never been connected to the internet. These offline, air-gapped systems significantly reduce the risk of online attacks, ensuring that your sensitive information remains inaccessible to malicious actors.
- Avoiding Compromised Devices: Be cautious about using devices that may be compromised or infected with malware. Even a seemingly secure device can harbor vulnerabilities. Prioritize dedicated devices or hardware wallets for seed generation and storage.
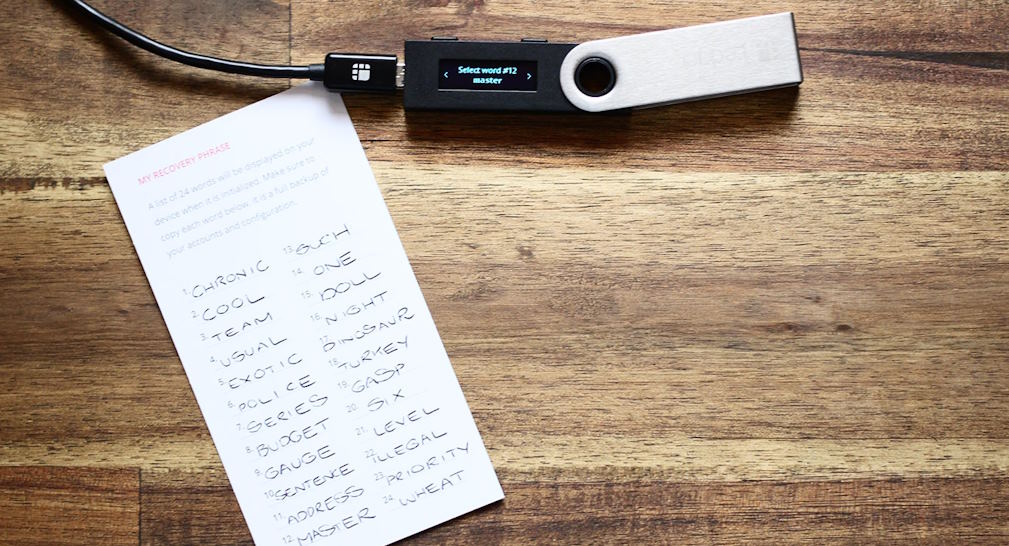
Importance of Writing Down Seeds
- Pen and Paper vs. Digital Storage: When recording your recovery seeds, stick to the old-fashioned method of pen and paper. This eliminates the risks associated with digital storage, such as exposure to hacks, viruses, or data corruption.
- Protecting Against Electronic Failures and Hacking: Unlike digital methods, a physical copy of your recovery seed is immune to electronic failures, glitches, and hacking attempts. This tangible approach ensures that your access to your cryptocurrency remains intact, even if your electronic devices fail.
Generating Recovery Seeds
The process of generating recovery seeds is a foundational step in fortifying the security of your cryptocurrency investments. Whether you’re a newcomer to the crypto realm or a seasoned enthusiast, understanding the methods of creating these seeds is essential for ensuring the safety of your digital wealth.
Using Reputable Wallet Providers
A reliable approach to generating recovery seeds is to rely on reputable wallet providers. Established cryptocurrency wallets often employ advanced cryptographic techniques to ensure randomness and unpredictability in seed generation. These providers adhere to rigorous security standards, minimizing the risk of compromised seed creation.
DIY Methods for Generating Seeds
For those seeking to take a hands-on approach to seed generation, do-it-yourself methods can offer a sense of control over the process.
- Dice Rolls and Randomness: A time-tested technique involves using physical dice to generate a sequence of random numbers. This randomness serves as the foundation for creating a highly secure recovery seed. By converting the dice rolls into corresponding words from a predefined word list (such as the BIP39 word list), you can craft a seed with a remarkable degree of unpredictability.
- Shuffling Words for Added Security: Another DIY method involves selecting words from a word list and shuffling them randomly. This process enhances security by introducing an extra layer of complexity to the seed generation process. The result is a unique and difficult-to-predict recovery seed.
Storing Recovery Seeds
After meticulously generating your recovery seeds, their secure storage becomes paramount. Safeguarding these access keys ensures that your cryptocurrency remains under your control, even in the most unforeseen circumstances. Let’s explore effective strategies for storing recovery seeds.
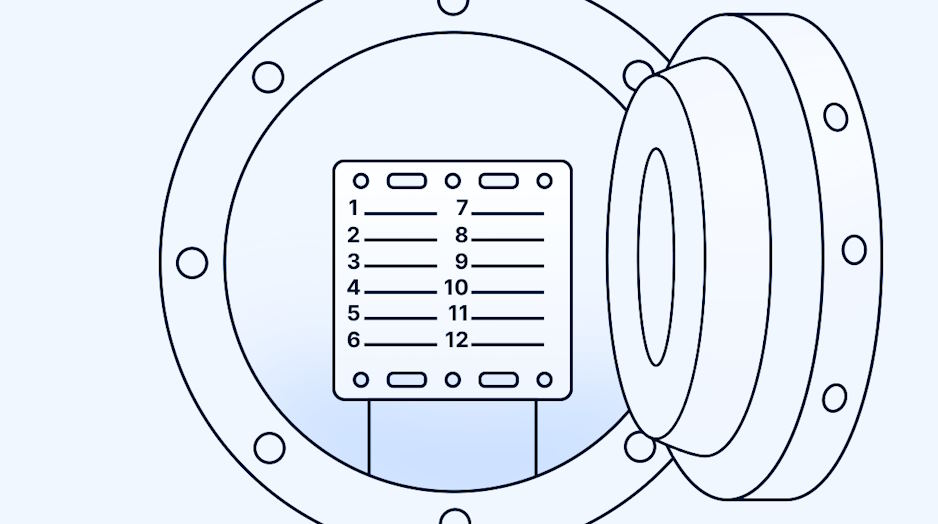
Physical Storage Options
- Safe Deposit Boxes: Many banks offer safe deposit boxes that provide an additional layer of protection against theft, fire, and other hazards. Storing your recovery seeds in such a box ensures their physical security, albeit with some reliance on external parties.
- Home Safes: Investing in a high-quality home safe can keep your recovery seeds close while offering protection against common household risks. Ensure the safe is fireproof, waterproof, and securely anchored.
- Hidden but Memorable Locations: Concealing your recovery seeds in unconventional yet memorable locations can be a creative solution. However, balance secrecy with ensuring that you won’t forget or lose the location over time.
Diversifying Storage Locations
To mitigate the risks associated with a single point of failure, consider diversifying the storage of your recovery seeds. Distributing copies across multiple physical locations, such as different safes or deposit boxes, reduces the impact of a single incident.
Encrypting Recovery Seeds
- Password-Based Encryption: Encrypt your recovery seeds with a strong passphrase before storing them physically. Memorize the passphrase or keep it in a separate secure location, adding an extra layer of protection against unauthorized access.
- Shamir’s Secret Sharing for Added Layers: Implementing Shamir’s Secret Sharing scheme involves splitting your recovery seed into multiple parts, distributing them among trusted individuals or storage locations. This approach significantly enhances security, as an attacker would need a specified number of shares to reconstruct the seed.